Verify
Verify is a data verification library that validates integrity, consistency, and privacy compliance between source and target systems during data movement, migration, platform upgrades, or replication.
It compares data at three levels — tables/files, records, and fields — and is PII-aware, meaning it applies different comparison rules depending on whether data has been masked. Tasks are created and executed through a web-based GUI — no scripting or command-line work is needed.
Core Capabilities
What Verify Detects
- Value mismatches
- Missing records (present in source, absent in target)
- Extra records (present in target, absent in source)
- Failed transformations
- PII masking failures
PII Comparison Logic
| Source Sensitive | Target Sensitive | Expected Result |
|---|---|---|
| ✅ | ✅ | Values must match exactly → PASSED |
| ❌ | ❌ | Values must match exactly → PASSED |
| ✅ | ❌ | Target is expected to be masked — values must be unequal → PASSED |
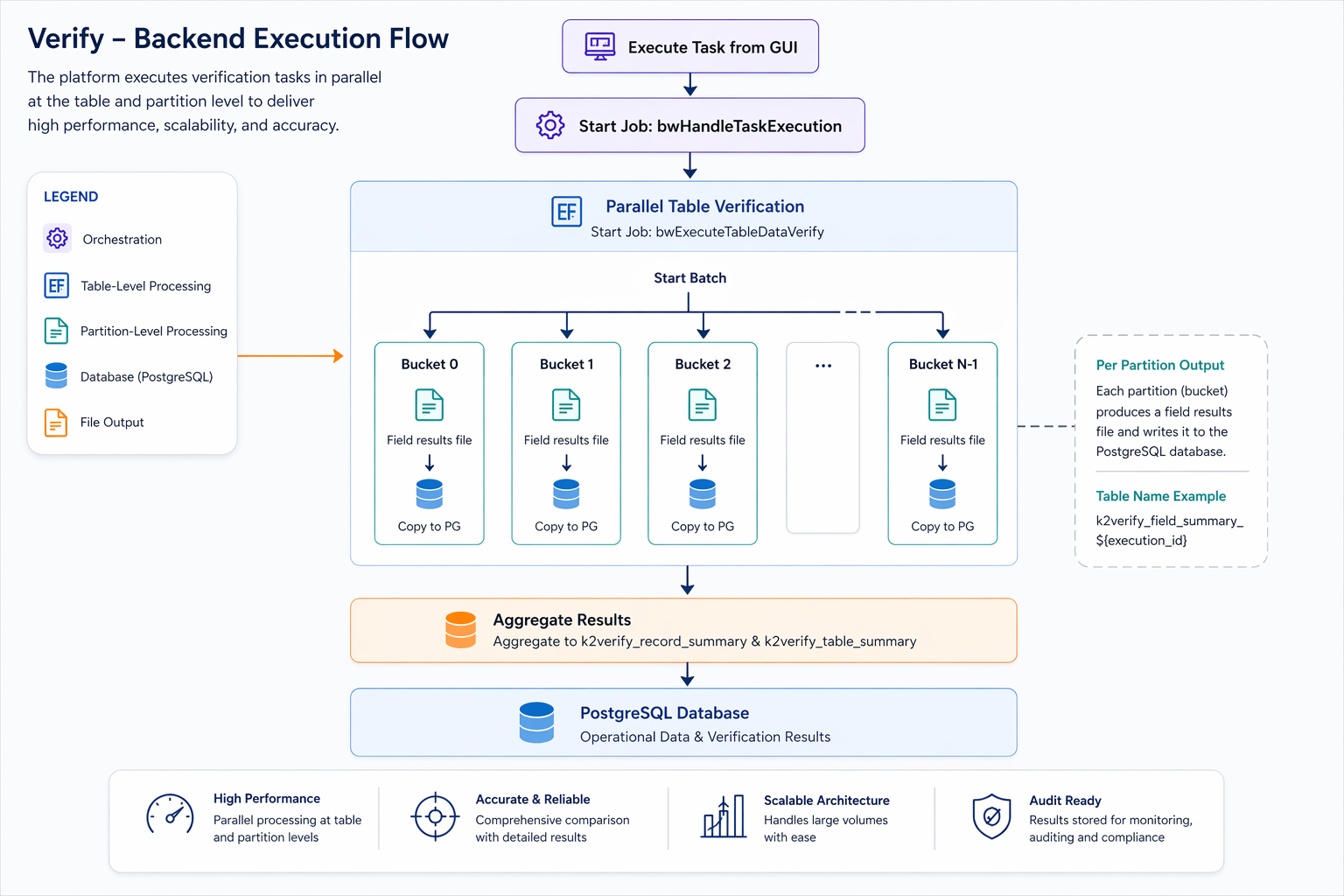
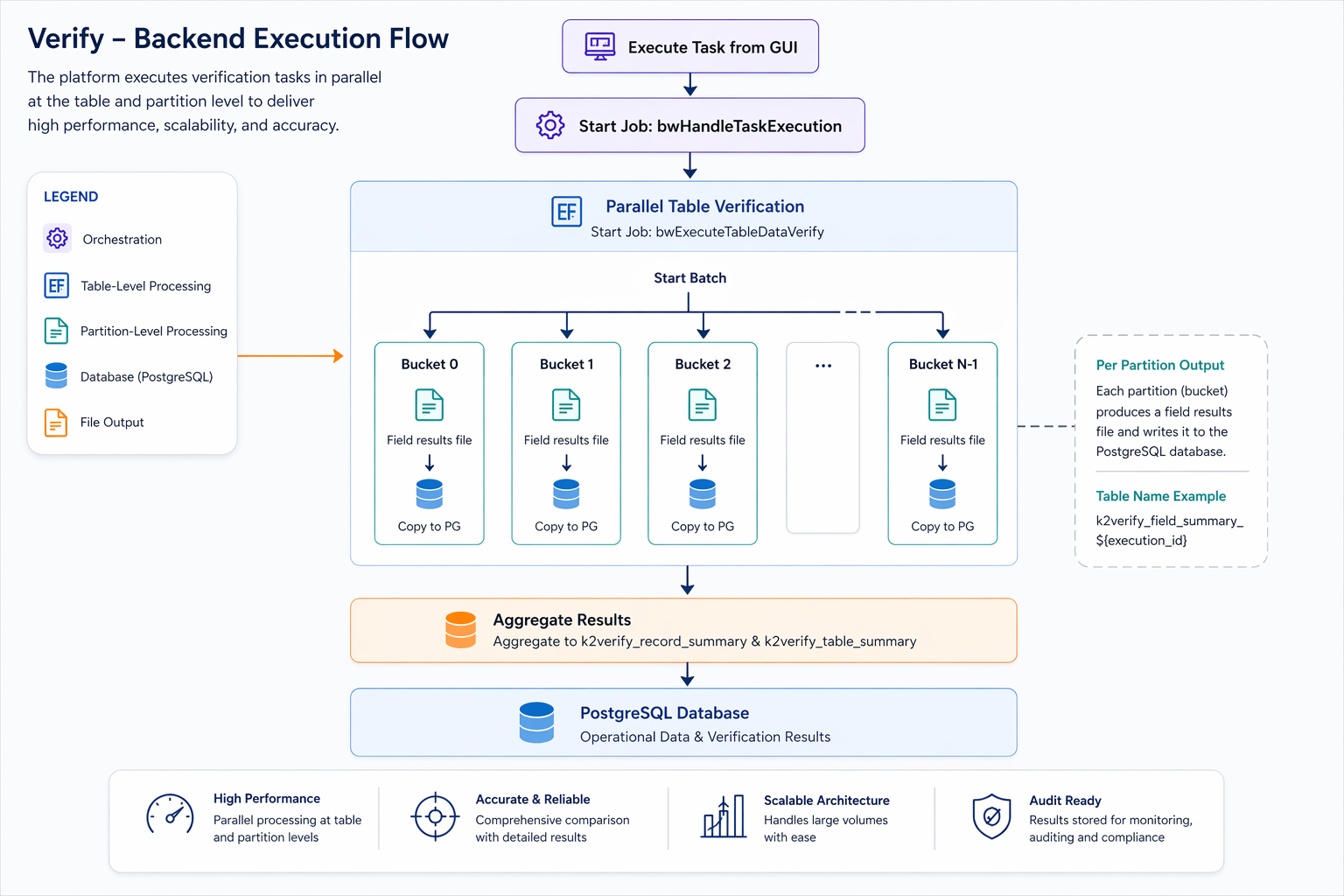
Verify Process Architecture
Verify
Verify is a data verification library that validates integrity, consistency, and privacy compliance between source and target systems during data movement, migration, platform upgrades, or replication.
It compares data at three levels — tables/files, records, and fields — and is PII-aware, meaning it applies different comparison rules depending on whether data has been masked. Tasks are created and executed through a web-based GUI — no scripting or command-line work is needed.
Core Capabilities
What Verify Detects
- Value mismatches
- Missing records (present in source, absent in target)
- Extra records (present in target, absent in source)
- Failed transformations
- PII masking failures
PII Comparison Logic
| Source Sensitive | Target Sensitive | Expected Result |
|---|---|---|
| ✅ | ✅ | Values must match exactly → PASSED |
| ❌ | ❌ | Values must match exactly → PASSED |
| ✅ | ❌ | Target is expected to be masked — values must be unequal → PASSED |
Verify Process Architecture